Recently a press release came around detailing how two UK-based researchers for IT security firm Pen Test Partners demonstrated ransomware for a smart thermostat. The researchers, Andrew Tierney and Ken Munro, used a smart thermostat with an LCD that runs Linux. The device also supports a SD card that stores user programs and custom graphics for the display.
Under test, the researchers showed that the thermostat does not check what file types it was executing. If that is the case, then, like and email client on a PC or through basic downloading, malicious files could infect the unit on site. And as the thermostat is online al la IoT, a crafty hacker could instruct it to execute a wee bit of ransomware.
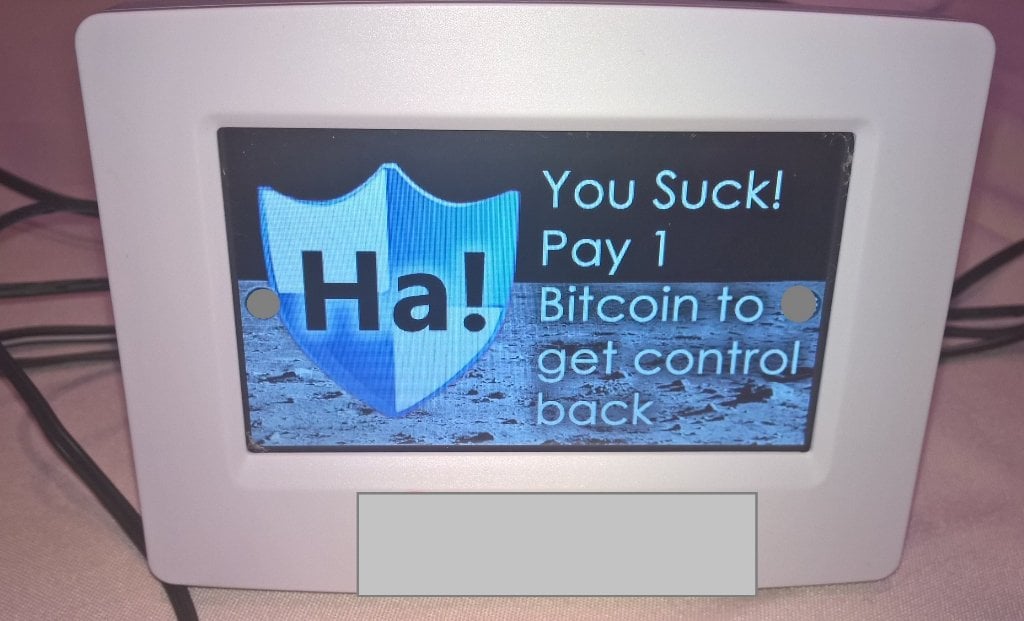
Did the researchers actually infect said smart thermostat? According to the circulated press material, they did not and their findings were theoretical in nature. As per the report, “The thermostat didn’t really check what kind of files it was running and executing. In theory, this would allow a malicious hacker to hide malware into an application or what looks like a picture and trick users to transfer it on the thermostat, making it run automatically.”
Obviously, if the device is executing programs from its SD card, one could easily put malware code on the card and wreak some havoc with the thermostat: hot, cold, hot, cold, $$$..... etc. And if the device is accessible remotely, the card could be just as easily accessed and messed with. Sounds like not much time and effort should’ve been spent establishing this, theoretically or otherwise.
Whenever security threats of this nature are discussed, the main culprit is always described as an anonymous hacker who spends most of his or her time on the Internet hacking into everything other people own. Okay, that’s often the case. But the IoT offers a lot more opportunities for a new wave of gremlins.
Two possibilities come to mind. The report cites one as what could happen when one purchases used smart devices. Retail outlets such as eBay and others offer many previously owned home improvement products including electronics. As smart thermostats are still pricey, it might be tempting to buy a used system in good condition for half the price of new. But that could be a dicey proposition if the previous owner knowingly or unwittingly has some malware installed.
Second idea, what if the new items, for whatever reason or by whatever means, come pre-hacked? What if someone at the manufacturer or at the retail outlet decides to tamper with the device for whatever reason? It could happen, and it has happened.
But we can’t be in a state of constant concern and not use these great devices. My question about the thermostat with the SD card is, outside of the operating program, what could, or better put why would anyone want to store any other information in their thermostat? Oh, I’m sure if some folks could hook their home heating/cooling systems into social media, they would do so in the blink of an eye, “gotta’ get that mass approval”.
An even better question is if you can put a program on that SD card or other storage media that will make the system do what the user wants at preset times during the day, or for actions to be taken at certain temperatures, lighting, etc., once it’s set and ready to go, why does it need to be on the Internet? Nothing better to do? Not enough distractions on that smartphone? ~MD